Horror films have attempted to scare us for decades with depictions of twisted villains, creepy monsters, and gruesome deeds, but their nightmare scenarios can't compete with the most competent directors around: ourselves. How many among us have been haunted by flickering shadows or sudden noises after the credits rolled? There is a reason why some of the most beloved scary movies apply exposition lightly and tension liberally: the true source of terror is not a ghastly visage—it is our mind pressing against the unknown.
Cybersecurity is the internet's version of a horror movie monster: at first, its mere mention fills us with dread as we imagine the worst possible scenario, but after exposing the gears and wires that give life to its animatronic limbs, we realize that the threat of cyberattacks is manageable after all. After learning why you could be at risk for a cyberattack and how you can protect yourself from different types of attacks, the thought of cybersecurity will spur you to confident action rather than send you cowering beneath the sheets.
Am I really at risk?
Perhaps the most enduring horror movie trope is characters splitting up to investigate something suspicious. If only they could see what the audience sees, they wouldn't underestimate the danger they were in! This article is your chance to learn from their mistakes and be prepared before you needlessly put yourself and your business at risk.
Cybercriminals can be motivated by notoriety, politics, or other emotional reasons, but the most common force driving cybercrime is personal gain. The object of a cyberattack is generally to make money as easily as possible and with as little risk as possible, which means the targets of cyberattacks may be a different demographic than you expect: Fortune 500 companies yield bounteous opportunities for wealth, but are secured too tightly; Mom and Pop are comparatively easier targets, but the potential for a windfall is iffy; however, small- to medium-sized businesses caught unprepared offer the perfect storm of opportunity and convenience. Without a dedicated IT department or software development team, a business faces increasingly more avenues of attack as time erodes their security standards.
Even if you believe a cybercriminal has little reason to target your business's data directly, consider what they stand to gain from stealing your users' data. In fact, most stolen data isn't even used by the original offender—it is more difficult to go through the effort of stealing someone's identity and more risky to rack up fraudulent credit card charges than it is to simply sell lists of personal data to other criminals willing to put in the effort.
How can I protect myself?
The best strategy for protecting yourself from the horrors which await you during the climax of a scary cybermovie is to simply read ahead in the script and prepare for each threat accordingly. There are many ways that your software, network, and internal accounts can be compromised, and understanding these attack vectors will allow you to secure the necessary measures to prevent villains from taking advantage of you.
Phishing
This is a type of scam involving an email which appears to be legit, but is actually designed to collect your personal information. A phishing email has the same design as an email from a bank, e-commerce site, or some other service, and asks you to log in to complete a simple task. However, clicking on a button or link in this email does not send you to your bank's website; instead, it links to a fake website that merely appears to be your bank's website, but is actually a fake lookalike website. Instead of logging you in to your account, this fake site collects your username and password...which the scammer can then use to access your real bank's website.
How does this type of scam affect your business? People have a tendency to reuse passwords or parts of passwords, making them easier to guess. If a phishing scam dupes you into coughing up your password to a fake e-commerce site, the integrity of your more sensitive accounts appears to be intact...unless you are reusing passwords. Learning one of your passwords could be a boon in a hacker's attempt to access the administrator account of your business, for example.
Sidestep phishing attacks by never clicking links in emails. If a service you use asks you to log in to your account for any reason, open up a new tab in your browser and manually type their website address. Additionally, use strong passwords for all of your accounts, business or otherwise! Read more about strong passwords in a section below.
Malware
Malware describes any software that performs a malicious action, such as granting outside access to your company's network, for example. In order for malware to compromise your company's security measures, a user within your network usually needs to initiate this software unwittingly. Similar to phishing, malware is often distributed as attachments to fake emails which, once again, appear to be from legitimate sources.
Remember: all computers contain sensitive data, because all computers are connected to the internet. Your bank account does not exist on your personal computer, but your personal computer can access your bank account via the internet. Similarly, malware installed on your personal computer at home may not have any sensitive business information stored on it (as it shouldn't), but any cross-pollination between your email accounts or websites you use between different computers is an angle that can be exploited by malware.
Deny malware a foothold by verifying the authenticity of the sender of any email which contains an attachment. Do not open any attachment unless you are confident its author intends no harm to you or your business. Additionally, be wary of downloading files from suspicious sites on the internet: the file new-horror-movie-1080p.exe may seem like an easy way to watch a recent film, but if you can't verify the authenticity of the site where you found it (and didn't recognize that 'exe' is not a video file format), do not open it.
Eavesdropping
This type of attack describes an outside party intercepting data as it travels across the internet. Attackers can easily glean usernames, passwords, and other sensitive information if they can view your network traffic. Eavesdropping attacks can be carried out if the attacker gains access to either your network (such as by cracking your wi-fi password), or by installing malware on a device on your network.
Since eavesdropping requires an attacker to be on the same network as you, free wi-fi networks present a significant security risk. It is fairly simple for anyone, attacker or not, to view any unsecured data transmitted over a network, which could include the usernames and passwords you type to log in to the services you use. Many websites and email clients encrypt (or scramble) requests for data, but using any application which does not encrypt communication will expose your data to anyone on the network who cares to listen.
Avoid eavesdropping attacks by installing a firewall to detect and protect you from suspicious network activity, and by installing a VPN to encrypt your traffic to and from the internet. Additionally, avoid any activity that involves transmitting unencrypted sensitive data over unsecured networks, such as at coffee shops and hotels.
An Aside on Strong Passwords
Many forms of cyberattacks revolve around the same principle: gaining access to your data. With access to your personal accounts, a cybercriminal can steal your identity and your credit card information, but with access to the right business accounts, a cybercriminal can steal and sell the identities of every user and employee. You owe it not just to yourself, but to everyone you've worked with and worked for to secure every account you have access to with a strong password.
The first step on the road to strong passwords is to never reuse a password. If a cybercriminal learns your AIM password from eavesdropping your network traffic at a coffee shop, they won't be able to access any of your other accounts unless you reuse that password.
The second step is to make your password difficult to guess. Using your name, your birthday, '12345', 'password', or any of the top 100 most-used passwords is easy street for gaining access to your accounts.
The third step is to make your password difficult to crack. Beyond guessing an easy password, the next recourse an attacker has is to attempt to brute force your password. This process describes checking up to 1 billion possible passwords per second against your account. This is a staggering number of combinations, but fear not! Increasing the length of your password has a surprisingly tangible effect on password cracking: with today's technology, it takes about 8 hours to crack any 8-character password (special characters or not), 8 days to crack any 10-character password, and 61 years to crack any 12-character password source. The way the math works is, each additional character increases the number of passwords at a far greater rate than expanding the password requirements to include a "special character" or number. So, in conclusion, aim for a longer password over a shorter one, or rely on a password manager to generate passwords for you.
Poorly-Made Software
While exploiting the ignorance of a company's employees is often an easy avenue for attack, depending on how thoroughly the writers of your software considered various security risks, your business's application itself may be a vector for attack. Clever criminals can exploit vulnerabilities in your software product to procure access to personal information using techniques such as SQL injection or cross-site scripting. Both attacks involve submitting malicious code through an ordinary form on your website, where an SQL injection attack attempts to modify or collect the data in your database, and a cross-site scripting attack aims to subvert the basic functions of your website while possibly also collecting user data in the process. Well-crafted software will prevent users from executing malicious code within your application.
Ensure your company's software product is airtight by hiring developers you trust. Much like anything else, you get what you pay for, which is especially true in the software industry. If a contract from a fly-by-night studio sounds too good to be true, it probably is. When vetting a software development studio, be sure to ask questions about how they approach security concerns in the software they write.
Distributed Denial of Service Attack
Sometimes personal gain can be framed as someone else's loss. Distributed Denial of Service Attacks (abbreviated as "DDoS") aim to deny site traffic—and, consequently, revenue or business—by flooding a website with fake traffic. Website servers can only handle so much bandwidth at a given moment, and a DDoS attack consumes all of the available bandwidth so that legitimate users aren't able to access the site. The motivations for DDoS attacks are as numerous as the businesses they affect, so it's difficult to predict how to sidestep the possibility of ever becoming a target; however, planning during the construction of your application will allow you to be prepared for the possibility.
Mitigate the threat of DDoS attacks by developing robust server architecture for your company's application. Even the best plans are prone to oversight and failure, however, so it’s important to have access to support to quickly address attacks on a case-by-case basis.
Physical Data Loss
An oft-overlooked cyberattack occurs in the physical realm: sensitive information can be lost when a laptop is stolen, misplaced, or its hard drive fails. Even the most robust network security can't prevent a cunning thief from swiping your laptop while you stand in line for a scone at the coffee shop!
As always, protect access to your devices with strong passwords or two-factor authentication, and encrypt your hard drives via settings offered by your operating system. Back up your data and store backups in a separate physical location (or the cloud) in case of fire or other disaster.
No Weak Links
Since many vectors for cyberattacks exist outside the bounds of your company's software product, any education you receive on cybersecurity has limited influence over the other attack vectors you work with. All it takes is a single foothold for a successful attack, so as your company grows, be sure to grow your cybersecurity education program accordingly.
Educate your employees in cybersecurity best practices by setting company policies. For example, require all company devices be locked with a passcode or two-factor authentication, and set password-creation rules that stand up to brute force attacks.
In Conclusion
The fear of cyberattacks is understandably amplified when you can't skip ahead to the end of the script, but understanding the villains' motivations and preparing a production checklist of best practices while on set are defenses sure to stymie the terror of the unknown. Educate yourself on the vectors through which you or your business can be targeted, take the necessary precautions, and change the trajectory of your business's genre from "horror" to "adventure."
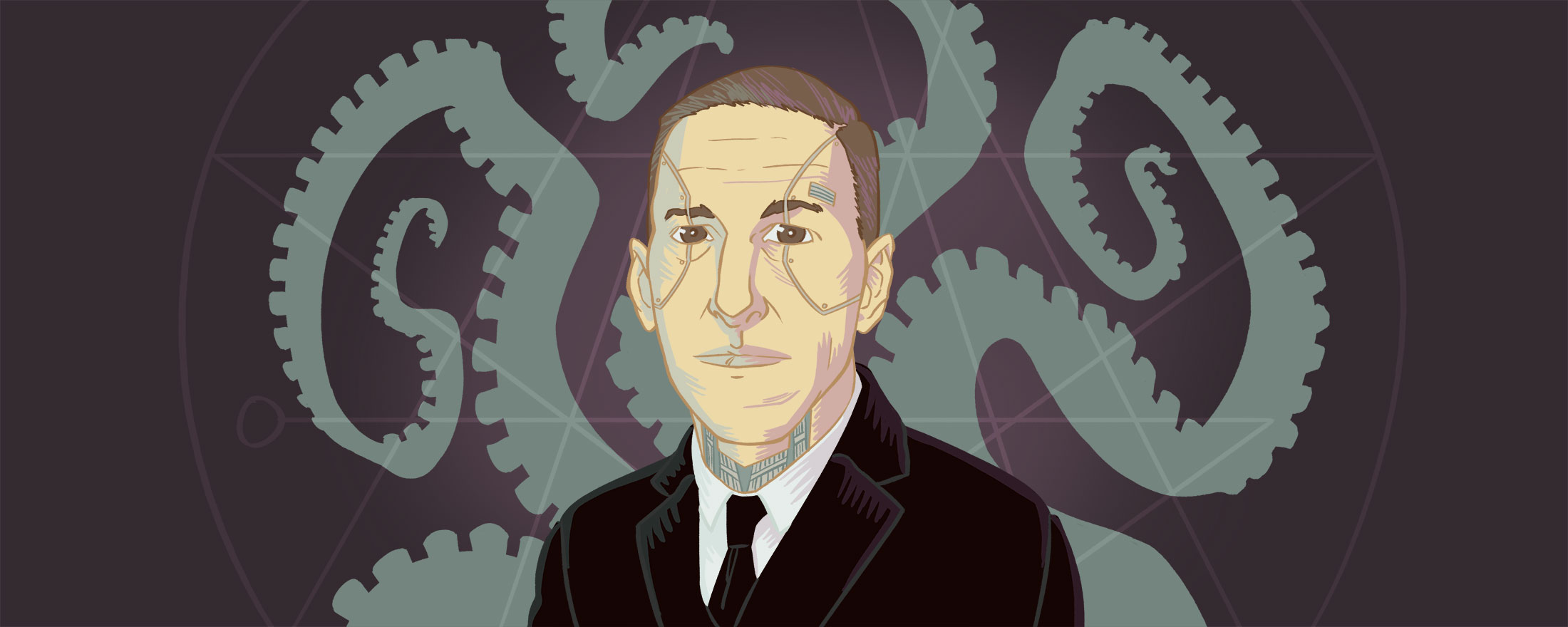
The art for this post depicts H.P. Lovecraft (author of short stories focusing on fear of the unknown) as a cyborg (a human with mechanical parts).